Managing data synchronization is more than just a technical challenge - it’s a compliance necessity. Regulations like GDPR, CCPA, and SOC 2 demand strict controls over how data moves between systems, protecting personal information, ensuring accountability, and minimizing risks of breaches or fines.
Here’s what you need to know:
- GDPR: Requires encryption, data minimization, and honoring deletion requests across systems. Fines can reach €20 million or 4% of global revenue.
- CCPA/CPRA: Grants California residents rights like data deletion, correction, and opting out of data sharing. Penalties start at $2,663 per violation.
- SOC 2: Focuses on securing synchronization processes, ensuring data integrity, and maintaining detailed audit trails. This requires assessing email platform compatibility to ensure secure data flow between systems.
Non-compliance can lead to hefty fines (e.g., Meta was fined €1.2 billion for GDPR violations in 2023). To stay compliant, implement encryption, access controls, and robust logging. Automating these processes can save time and reduce risks as global data regulations grow stricter.
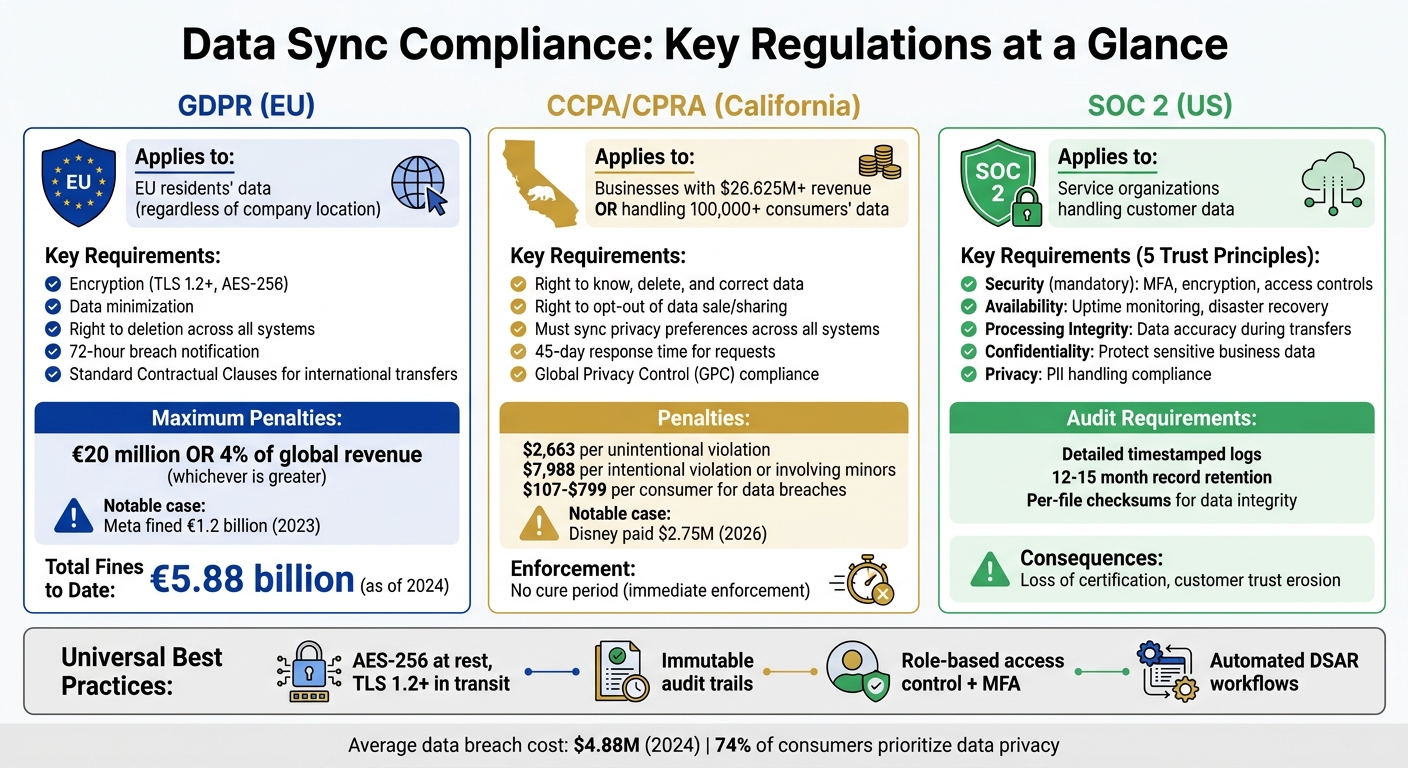
GDPR, CCPA, and SOC 2 Data Sync Compliance Requirements Comparison
Regulatory Requirements for Data Security | Exclusive Lesson
sbb-itb-6e7333f
GDPR Requirements for Data Synchronization
The General Data Protection Regulation (GDPR) lays out strict rules for managing personal data as it moves between systems. Whether you're syncing data from a CRM to a enterprise email marketing solutions or between cloud environments, these rules apply. And it doesn’t matter where your company is located - if you’re handling data from EU residents, GDPR applies.
GDPR Principles and What You Must Do
GDPR outlines seven key principles that directly impact data synchronization processes. Let's break them down:
- Lawfulness, fairness, and transparency: You need a clear legal basis - like user consent or a contractual need - before transferring data between systems.
- Purpose limitation: Data collected for one reason (like customer emails for order confirmations) cannot be reused for something else (e.g., training an AI system) without explicit permission.
"Keeping lots of data 'just in case' or to 'optimize performance' clashes directly with the purpose limitation and data minimization principles in the GDPR" – Spanish Data Protection Authority
- Data minimization: Only transfer the data that’s absolutely necessary. Bulk transfers that include unnecessary data violate this rule.
- Accuracy: Any updates, such as corrections or deletions, must be reflected across all connected systems without delay.
- Storage limitation: Aim for systems that process data temporarily - like in-memory processing - and delete it immediately after synchronization.
- Integrity and confidentiality: Protect data during synchronization using encryption and strict access controls to prevent breaches or unauthorized access.
- Accountability: Track and document every data movement. This includes logging details like where the data was sent, when it was transferred, and which safeguards were in place.
Technical Measures for GDPR Compliance
To align with GDPR principles, businesses must implement strong technical measures. Article 32 of GDPR highlights specific security requirements:
- Encryption: Use TLS 1.2+ for data in transit and AES-256 for data at rest. Regularly test your encryption methods. A 2025 analysis revealed that over half of 5,200 open-source integrations used insecure static secrets, while only 8.5% employed secure OAuth methods.
- Access controls: Follow the least-privilege principle. This means adopting scoped OAuth permissions, isolating data at the tenant level, and enforcing multi-factor authentication for those managing synchronization processes.
"Compliance happens at the architecture level, not the contract level" – Jim Kutz, Airbyte
- International transfers: If transferring data to countries without an EU adequacy decision (like the U.S.), Standard Contractual Clauses (SCCs) alone aren’t enough. Conduct a Transfer Impact Assessment to evaluate the destination country's surveillance laws and add safeguards like field-level encryption.
- Audit trails: Keep detailed logs showing what data was synced, when, and by whom. Experts recommend retaining these records for 3 to 5 years.
GDPR Penalties and How They're Enforced
National Data Protection Authorities (DPAs) ensure GDPR compliance through fines, audits, and corrective measures. Fines can be severe:
- Up to €10 million or 2% of global annual turnover for administrative issues like poor record-keeping.
- Up to €20 million or 4% of global annual turnover for serious violations, such as unlawful data transfers.
A notable case occurred in May 2023, when the Irish Data Protection Commission fined Meta Platforms Ireland Limited €1.2 billion. Meta had continued transferring EU residents' data to the U.S. using SCCs, despite the Schrems II ruling, which deemed U.S. surveillance protections inadequate. This fine remains the largest GDPR penalty to date and included an order to stop future data transfers.
Beyond fines, DPAs can issue corrective orders, including halting data synchronization altogether. Organizations must also report personal data breaches within 72 hours and design systems to respond to user rights - like erasure requests - within one month.
With nearly 100 countries enforcing data privacy laws, GDPR penalties have been mounting. In 2024 alone, regulators issued €1.2 billion in fines, contributing to a total of €5.88 billion since GDPR’s inception. These figures highlight why compliance is essential for any data synchronization process.
SOC 2 Requirements for Data Synchronization
SOC 2, established by the American Institute of CPAs (AICPA), is an auditing standard created to evaluate how service organizations manage and secure customer data. While regulations like GDPR and CCPA focus on data privacy, SOC 2 emphasizes the integrity of processes. Specifically, it assesses whether your systems safeguard data integrity and security during synchronization. Unlike GDPR’s strict focus on personal data, SOC 2 zeroes in on operational integrity.
The 5 SOC 2 Trust Service Principles
SOC 2 audits revolve around five Trust Service Principles. Among these, only Security is mandatory, while the others depend on your business model and customer requirements:
-
Security
Security is the cornerstone of SOC 2 compliance. It ensures that synchronization systems are protected from unauthorized access. Measures like firewalls, multi-factor authentication (MFA), strict access controls, and encrypted data transfers are crucial. Logging every transfer adds an extra layer of accountability. -
Availability
This principle ensures that your synchronization systems remain operational. It involves monitoring uptime, implementing disaster recovery plans, and establishing clear procedures to restore services after outages. -
Processing Integrity
Processing Integrity focuses on the accuracy and completeness of data as it moves between systems. Techniques like input validation, error-handling protocols, and checksums help prevent corruption during transfers. -
Confidentiality
Confidentiality safeguards sensitive business information, such as intellectual property or internal documents, during synchronization. This requires encryption both in transit and at rest, alongside secure deletion protocols once the data is no longer needed. -
Privacy
Privacy applies when synchronizing Personally Identifiable Information (PII). It ensures compliance with privacy laws and policies by emphasizing user consent, proper notification, and data minimization practices.
"Including more Trust Services Criteria does not necessarily mean stronger security; it means broader assurance coverage aligned to your business model and customer expectations." – Rachna Dutta, Infosec Consultant, Sprinto
For organizations new to SOC 2, it’s best to start with the mandatory Security principle and gradually incorporate additional principles as your compliance strategy evolves.
Logging and Record Retention Requirements
Once these principles are in place, robust logging becomes essential to demonstrate compliance over time.
SOC 2 audits require detailed evidence showing that controls are consistently applied. This includes timestamped audit trails documenting every synchronization event - what data was synced, when it happened, who initiated it, and whether it succeeded.
Using per-file checksums during data transfers can provide mathematical proof that the data remained intact. Many modern tools can automatically generate compliance reports, streamlining this process.
Audit evidence typically needs to be retained for 12 to 15 months. However, many integration platforms default to retaining transaction logs for only 30 to 90 days. It’s crucial to align your retention policies with audit requirements while adhering to data minimization principles.
Avoid retaining unnecessary data, as it increases the risk of breaches. A notable example is Blackbaud’s 2024 settlement with the California Attorney General. The company faced a $6.75 million settlement after retaining consumer data longer than necessary, including data from former clients. This was in addition to earlier settlements totaling $49.5 million with multiple states and $3 million with the SEC.
To reduce compliance risks, consider adopting "zero-storage" architectures. These systems process data in memory and discard it immediately after synchronization, eliminating the need for data-at-rest management and reducing the likelihood of shadow data accumulation.
CCPA and State Privacy Laws for Data Synchronization
The California Consumer Privacy Act (CCPA), along with its 2023 update under the California Privacy Rights Act (CPRA), places strict requirements on how businesses manage synchronized data. These laws focus on consumer rights, ensuring that data remains consistent across interconnected systems like CRMs, ERPs, and email marketing platforms. Notably, the CCPA now extends to employee data, meaning HR systems syncing with ERPs also fall under its purview.
The law applies to businesses meeting certain thresholds: annual gross revenues exceeding $26.625 million (starting January 1, 2025) or handling the personal data of 100,000 or more consumers or households annually. If your operations involve moving data across these boundaries, compliance isn't optional. To align with these regulations, understanding the specific rights granted to consumers under the CCPA is essential.
Consumer Rights Under CCPA
The CCPA grants consumers a range of rights that directly impact how data synchronization is handled:
- Right to Know: Businesses must compile data from all synchronized systems - such as CRMs, ERPs, and analytics platforms - to provide a complete report upon request.
- Right to Delete: When a deletion request is made, it must cascade across all systems, including those managed by service providers and contractors.
- Right to Correct: Introduced by CPRA, this ensures that corrections made in one system (e.g., updating an email address in a CRM) are reflected across all interconnected systems to avoid discrepancies.
- Right to Opt-Out of Sale or Sharing: If a consumer opts out in one system, such as a CRM, that status must be synchronized across other platforms like ERPs and marketing tools.
- Right to Limit Use of Sensitive Personal Information: Sensitive data (e.g., geolocation, genetic information) must only be used for essential purposes.
- Right to Non-Discrimination: Consumers exercising these rights cannot face penalties such as service denials or price changes. Businesses must also respond to verified requests within 45 days, with a possible 45-day extension if necessary.
To comply with these rights, businesses need to implement specific technical measures in their data synchronization processes.
Technical Methods for CCPA Compliance
Effective compliance with the CCPA depends on robust technical controls within your synchronization architecture:
- Field-Level Masking: Limit synchronization of sensitive fields unless absolutely necessary.
- Centralized Privacy Orchestration: Use a single control layer to automate tasks like data classification, consent management, and handling deletion or correction requests.
- Real-Time Data Retrieval: Instead of replicating data, retrieve it live using pass-through APIs to reduce the scope of stored information.
- Encryption Standards: Use TLS encryption for API communications and AES-256 for any temporary storage, adhering to CPRA's data minimization principles.
- "Do Not Sell" Synchronization: Ensure this status is a primary field in two-way data flows to prevent unintentional sharing of restricted data.
Starting January 2026, businesses must also comply with ADMT regulations, which require transparency in automated profiling logic and outcomes.
"The path for a consumer to exercise a more privacy-protective option shall not be longer or more difficult, or time-consuming than the path to exercise a less privacy-protective option." – 11 Cal. Code Regs. § 7004
The penalties for non-compliance are steep, as detailed below.
CCPA Penalties and State Enforcement
From 2026 onward, the California Privacy Protection Agency (CPPA) and the Attorney General will oversee enforcement. Penalties include $2,663 per unintentional violation and $7,988 for intentional violations or those involving minors. Data breaches involving non-encrypted or non-redacted information can result in statutory damages ranging from $107 to $799 per consumer, per incident. Notably, California eliminated its 30-day "cure period", allowing immediate enforcement.
High-profile cases illustrate the consequences of non-compliance:
- The Walt Disney Company: Paid $2,750,000 in February 2026 after failing to honor opt-out requests across Disney⁺, Hulu, and ESPN⁺ platforms.
- PlayOn Sports: Fined $1,100,000 in March 2026 for privacy violations involving student data, requiring an overhaul of its synchronization practices.
- Ford Motor Company: Paid $375,000 in March 2026 for complicating the opt-out process, hindering consumers from syncing their privacy preferences.
- Tractor Supply Company: Settled for $1,350,000 in September 2025 for failing to maintain effective opt-out mechanisms and sharing data without proper contractual protections.
Other states impose varying penalties. For instance, Colorado caps fines at $20,000 per violation, while Florida's base penalty is $50,000, with treble damages for cases involving children. Unlike California, states like Texas and Maryland still offer cure periods of 30 and 60 days, respectively.
For data brokers, California's DELETE Act, effective January 1, 2026, introduces the DROP platform. Brokers must process deletion requests every 45 days via this platform and pay an annual $6,000 registration fee to the CPPA.
To minimize risks, businesses should:
- Update contracts with service providers to ensure downstream recipients honor deletion and correction requests.
- Implement Global Privacy Control (GPC) signals across all synchronized platforms as valid opt-out requests.
- Automate data cleanup tasks to avoid retaining information longer than permitted and exclude "do not sell" contacts during synchronization cycles.
Technical Controls for Compliance
Strong technical controls are essential for safeguarding data during synchronization and ensuring the availability of detailed audit trails. By focusing on encryption, monitoring, and data transformation, you can strengthen your compliance strategies.
Encryption and Access Management
To protect data at rest, AES-256 encryption is the industry standard across synchronized systems. For data in transit, TLS 1.2 is the minimum recommended by NIST, with TLS 1.3 preferred for better protection against man-in-the-middle attacks during API calls and data transfers. Sensitive fields, such as customer_email, should be encrypted at the field level using AES-256 before any external transfers.
Role-Based Access Control (RBAC) ensures users and automated processes only access the data necessary for their specific roles, adhering to the principle of least privilege. Adding multi-factor authentication (MFA) to all access points further secures personal data storage and management systems. For synchronization processes requiring elevated credentials, Privileged Access Management (PAM) solutions provide audit logs for better traceability.
"Privacy without security is meaningless. Even the most privacy‐conscious data model can be rendered irrelevant by a breach."
– Sudhir Mangla
Access control measures can be enhanced with rotating API keys and token-based authentication, which allows for immediate revocation of individual tokens without disrupting entire systems. Tools like AWS KMS or HashiCorp Vault can help automate the rotation, storage, and auditing of keys.
Logging and System Monitoring
Encryption and access controls are only part of the equation - comprehensive logging ensures every data movement is accounted for. By maintaining detailed logs, organizations can establish a "chain of custody" to track what data was accessed, when, and by whom. This is critical for meeting SOC 2 and GDPR accountability standards. Logs should be stored in write-once, read-only storage to prevent tampering or unauthorized deletion. For compliance, HIPAA requires logs to be retained for six years, while SOC 2 mandates retention for 12–15 months.
Instead of logging sensitive data, record specific actions (e.g., "User Address Updated") to minimize privacy risks. To ensure log integrity, use SHA-256 hashing and RSA digital signing to detect tampering or forgery. Tools like Amazon EventBridge can enable automated responses to compliance-related events, further enhancing monitoring capabilities.
Granular logs also help meet GDPR’s 72-hour breach notification requirement (Article 33) by quickly identifying the scope and timeline of unauthorized access. Regular audits of SaaS-to-SaaS integrations can prevent personal data from being synchronized without proper oversight.
Data Transformation and Deletion Tracking
Pseudonymization can protect privacy while retaining analytical value by converting direct identifiers (like user IDs) into UUIDs and storing mapping keys separately in a secure vault. For deletion requests, crypto-shredding is an effective method: by encrypting data with a unique user-specific key and deleting that key, the data becomes unreadable. This approach aligns with GDPR’s "right to erasure" requirements, even for backups and logs.
Webhooks can automate "Right to Be Forgotten" requests, triggering deletion across distributed systems, including search indices and backups. For distributed architectures, the saga pattern helps coordinate deletion across multiple microservices, using retry mechanisms like exponential backoff to ensure completion. To verify data integrity during and after migration, perform per-file checksum comparisons.
Regional data planes are another critical measure, ensuring raw personal data stays within specific jurisdictions (e.g., the EU), while only anonymized or aggregated data is shared globally. Considering the average data breach cost in 2024 was $4.88 million, these technical controls are essential for protecting both compliance efforts and business operations.
Conclusion: Meeting Data Sync Compliance Requirements
Key Takeaways for Enterprises
To avoid the risks and penalties associated with non-compliance, businesses need to prioritize efficient compliance strategies. Data synchronization compliance not only safeguards customer trust but also protects revenue. For example, GDPR violations can result in fines as high as €20 million or 4% of annual revenue, whichever is greater. By the end of 2025, GDPR fines had already surpassed €4.5 billion. Similarly, CCPA/CPRA violations can cost up to $7,500 per record, with no cap on the total penalty. Non-compliance with SOC 2 standards can lead to the loss of certifications and eroded customer confidence.
Privacy-conscious companies often see tangible benefits, such as reducing sales cycle delays by up to 80% - from an average of 16.8 weeks down to just 3.4 weeks. With 74% of consumers expressing a strong preference for data privacy and 91% placing trust in companies that are transparent about their data practices, compliance is directly linked to business growth. Adopting a "highest common denominator" approach, where the strictest regulatory requirements are used as a baseline, simplifies global operations and minimizes regulatory complexity.
Steps to Begin Compliance Implementation
To turn these principles into action, start by mapping your data flows. Use automated tools to classify and track how personal information enters, moves through, and exits your systems. This can cut audit preparation time by up to 68%. Strengthen your systems with robust encryption and multi-factor authentication to protect sensitive data. Establish immutable audit trails to log who accessed data, when, and under what legal basis - without storing sensitive information in the logs themselves. Additionally, sign Data Processing Agreements (DPAs) with every third-party vendor involved in data synchronization to ensure they meet compliance standards.
Prepare workflows to handle Data Subject Access Requests (DSARs) within the required timeframes: 30 days for GDPR and 45 days for CCPA. By 2026, the world will generate 463 exabytes of data daily, making manual compliance unsustainable. Automation isn't just a helpful tool - it’s a necessity for scaling compliance with GDPR, CCPA, and SOC 2 requirements efficiently.
FAQs
How do I know which data syncs are in scope for GDPR or CCPA?
To figure out if your data sync is subject to GDPR or CCPA, you need to ask a critical question: Does it involve the personal information of individuals from the EU or California? If the answer is yes, these regulations likely apply.
Once identified, compliance becomes essential. Start by reviewing the key requirements of each regulation. This includes understanding the purpose of data processing, securing proper consent, and respecting the rights of data subjects. To make this process more manageable, use compliance guides or checklists tailored to GDPR and CCPA standards. These tools can help ensure you're meeting all necessary obligations.
What’s the fastest way to handle deletion requests across all synced systems?
To process deletion requests efficiently, start by confirming the identity of the person making the request. Next, identify and remove all personal data from the applicable systems, ensuring you respect any legal exceptions and meet required deadlines. Stay aligned with regulations such as GDPR and CCPA by implementing streamlined procedures to handle these requests effectively.
How can we meet audit log retention needs without storing too much personal data?
To address audit log retention requirements while keeping personal data to a minimum, consider these strategies:
- Keep only essential information: Retain data that is strictly necessary for auditing purposes, avoiding the storage of unnecessary personal details.
- Automate redaction and deletion: Implement automated systems to redact sensitive data and delete outdated information promptly.
- Set appropriate retention periods: Align retention timelines with legal and regulatory obligations, ensuring they are neither too short nor excessively long.
These methods not only reduce unnecessary data storage but also help maintain compliance with relevant regulations.


