Email APIs are critical for businesses, enabling smooth communication through transactional emails, marketing campaigns, and automated workflows. However, they are increasingly targeted by cyberattacks, with API breaches costing an average of $6.1 million per incident. The FBI reports $51 billion in losses from business email compromise since 2013, including $2.77 billion in 2024 alone. This guide provides a step-by-step plan to handle email API security incidents effectively, helping minimize financial and reputational risks.
Key Takeaways:
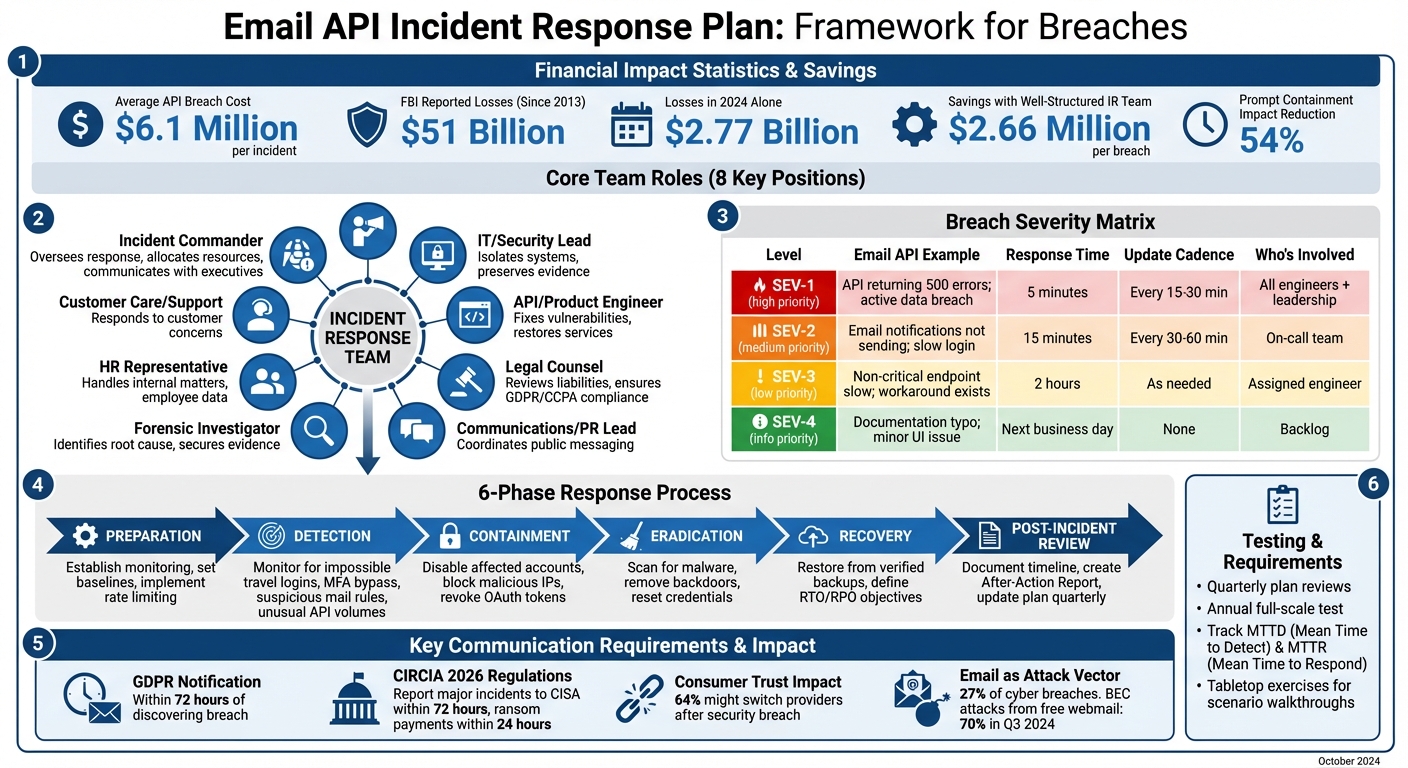
- Team Roles: Clearly define roles like Incident Commander, IT Lead, Legal Counsel, and PR Lead.
- Breach Severity Matrix: Classify incidents (SEV-1 to SEV-4) to prioritize response efforts.
- Communication Protocols: Use secure, out-of-band tools and pre-approved templates for crisis messaging.
- Response Phases: Prepare, detect, contain, eradicate, recover, and review incidents.
- Testing: Run simulations and review plans quarterly to stay prepared.
Email APIs are essential for business continuity, making strong incident response plans and regular testing indispensable for mitigating growing cybersecurity threats.
Email API Incident Response Plan: 6-Phase Process with Team Roles and Severity Matrix
Unmasking the Invisible Threat: Defend Your APIs Before Attackers Do
sbb-itb-6e7333f
Key Elements of an Email API Incident Response Plan
When it comes to tackling email API breaches, having a solid incident response plan is non-negotiable. This plan should clearly define team roles, outline how to assess incident severity, and establish communication protocols to ensure swift and effective action. According to BreachResponseFirms.com:
A well-structured incident response team saves $2.66 million per breach. Define roles before crisis hits - not during.
Acting quickly can make a huge difference. Organizations that contain a breach promptly can cut the overall impact by 54%.
Assigning Team Roles and Responsibilities
Start by pulling together a core team of 6–8 people, each with a specific role to play. Here’s a breakdown of key positions:
- Incident Commander: Oversees the entire response, allocates resources, and handles communication with executives.
- IT/Security Lead: Manages technical tasks like isolating systems and preserving evidence.
- API/Product Engineer: Fixes vulnerabilities and restores affected services.
- Legal Counsel: Reviews liabilities and ensures compliance with regulations like GDPR or CCPA.
- Communications/PR Lead: Coordinates public messaging, including updates to customers and media.
- Forensic Investigator: Often an external expert who identifies the root cause and secures evidence for legal needs.
- HR Representative: Handles internal matters, especially if employee data is involved.
- Customer Care/Support: Responds to customer concerns during the incident [10, 13].
To keep things organized, use a RACI matrix to clarify responsibilities during each phase of the response. Also, maintain a secure, offline contact list of team members and external partners. Negotiating retainer agreements with external experts in advance can help reduce costs when incidents occur.
Once roles are defined, the next step is establishing a system to classify the severity of breaches.
Building a Breach Severity Matrix
A severity matrix helps your team respond quickly and appropriately. For email APIs, you can use a four-level system (SEV-1 to SEV-4) based on factors like the type and amount of data exposed or whether core functions (like sending emails) are affected [14, 13].
| Level | Email API Example | Response Time | Update Cadence | Who's Involved |
|---|---|---|---|---|
| SEV-1 | API returning 500 errors for all requests; active data breach | 5 minutes | Every 15–30 minutes | All engineers + leadership |
| SEV-2 | Email notifications not sending; login functioning but extremely slow | 15 minutes | Every 30–60 minutes | On-call team |
| SEV-3 | Non-critical API endpoint responding slowly; workaround exists | 2 hours | As needed | Assigned engineer |
| SEV-4 | Documentation typo; minor UI alignment issue in dashboard | Next business day | None | Backlog |
Always assign a severity level within two minutes of detecting an issue. It’s better to overestimate and downgrade later than to underestimate and risk escalation. Automated monitoring tools can help here - if an error rate for HTTP 5xx responses spikes over 50%, for instance, a SEV-1 alert should be triggered.
Setting Up Communication Protocols
Effective communication is critical during an incident. Assign a single point of contact for all external communication to avoid mixed messages. Use out-of-band tools like Mattermost to ensure communication stays functional, even if your main network is compromised. Create a stakeholder map that includes internal teams, executives, customers, external partners, regulators, and the media [15, 16, 17].
Pre-approved templates for scenarios like data breaches or service outages can save valuable time during a crisis [16, 17]. For example, GDPR requires notifying authorities within 72 hours of discovering a breach involving personal data.
Paul Kirvan, a Technical Writer and Consultant, emphasizes:
The frequency, quality and content of these communications have a significant effect on public perception.
Regular practice through tabletop exercises ensures everyone, especially spokespersons, is prepared. Automated tools like PagerDuty can also help quickly bring the team together. Keep in mind that trust is fragile - 64% of consumers might switch providers if a security breach damages their confidence.
Step-by-Step Response Process for Email API Breaches
Building on clearly defined roles and severity matrices, the following phases outline a structured response plan. This multi-phase approach helps limit the impact of a breach.
Preparation Phase
The first step is to establish monitoring systems and set behavioral baselines before any incident occurs. This means using API-native monitoring tools (like Microsoft Graph or Google Workspace APIs) and leveraging AI-driven solutions to understand normal behaviors. Adding rate limiting to API endpoints is another essential step to prevent data exfiltration.
Why is this important? Because email remains a common attack vector, linked to 27% of breaches. These proactive measures ensure the system is ready to quickly identify and isolate potential threats.
Detection and Containment
Once a breach occurs, fast detection is critical. Look for signs such as impossible travel logins, MFA bypass attempts, suspicious mail rules, unusual API call volumes, unauthorized IP addresses, or odd login times. When anomalies are detected, immediate actions include disabling affected accounts, blocking malicious IPs, and revoking compromised OAuth tokens and API keys.
Mick Leach, an Incident Response Expert at Abnormal Security, highlights the importance of acting quickly:
What you do when you first discover the attack will decide how costly and far-reaching the damage is.
Take Valvoline as an example. In 2024, they implemented an automated phishing triage system using API-based email security. This saved them 480 analyst hours per month by automating the review of suspicious emails reported by employees. Tools like SIEM and SOAR can also automate responses, such as isolating users or blocking domains as soon as threats are identified.
Once the immediate threat is contained, the focus shifts to removing malicious elements and restoring normal operations.
Eradication, Recovery, and Post-Incident Review
After containment, the next steps involve scanning for malware, removing backdoors, resetting compromised credentials, and restoring data from verified backups. It's essential to define clear Recovery Time and Recovery Point Objectives to minimize downtime.
Equally important is learning from the incident. Document the timeline and key takeaways in an After-Action Report. Regularly update your response plan - ideally every quarter - and conduct tabletop exercises to improve detection and recovery strategies. This is particularly important given that, as of 2025, 65% of organizations still struggle to fully recover from past breaches.
Finally, evaluate the "explainability" of your detection tools. Understanding why certain anomalies were flagged - or missed - can help fine-tune your AI-driven security systems for better future performance.
Testing and Updating Your Incident Response Plan
Creating an incident response plan is just the first step - its effectiveness depends on regular testing and updates. Without these, even the most detailed plan can fall apart when faced with an actual breach.
Running Email API Breach Simulations
Once roles and response steps are defined, simulations are essential to evaluate how well the plan works under pressure. Start with tabletop exercises, where your team walks through hypothetical scenarios. These exercises are low-cost and help clarify everyone's responsibilities [24, 25]. For instance, you could simulate a CEO impersonation attack during a known executive absence, using urgent language to request a wire transfer. This helps assess how quickly the team identifies and reacts to the threat.
After tabletop discussions, move to practical drills that test technical systems. Tools like mailbox simulators - such as Amazon SES's testing addresses - can verify whether monitoring systems detect API event notifications properly without risking your sender reputation. For account takeover scenarios, simulate access from geographically impossible locations to ensure automated account locks activate within 30 minutes.
Billy Gouveia from Surefire Cyber highlights the value of hands-on practice:
Practicing an Incident Response Plan [...] in real-time is the only way to know that it will work. It's through these exercises that stakeholders can obtain the required understanding of the overall response strategy as well as the desired confidence in the organization's cyber resilience.
Track metrics like Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) to measure your team's efficiency. Include cross-functional teams to test broader scenarios, such as verifying vendor compromises. This approach is crucial, especially since nearly 70% of BEC attacks in Q3 2024 originated from free webmail domains, making them harder to identify.
These simulations provide actionable insights, which can guide updates during regular plan reviews.
Regular Plan Reviews and Threat Monitoring
Simulations are just one part of the process - routine reviews ensure your plan stays effective against evolving threats. Schedule quarterly reviews of your response plan and conduct a full-scale test annually [27, 12, 25]. The threat landscape is constantly shifting; for example, email was the attack vector in 27% of cyber breaches, and attackers now use generative AI to craft sophisticated phishing campaigns.
Update your plan immediately after significant incidents or organizational changes [23, 27]. Post-incident reviews should include a corrective-action register with clear ownership and deadlines. In 2026, pay close attention to emerging risks like AI-generated deepfakes targeting executives or employees accidentally sharing sensitive data with unauthorized AI tools.
Under the 2026 CIRCIA regulations, entities must report major cyber incidents to CISA within 72 hours and ransom payments within 24 hours. Your plan should include these timelines explicitly. Nandor Katai from Valydex stresses this point:
An incident response plan is effective only when authority, timing, and evidence requirements are explicit. The goal is not perfect analysis in the first hour; the goal is controlled containment, continuity, and decision quality under pressure.
Stay ahead of attackers by subscribing to threat intelligence feeds for updates on new compromise indicators and evolving tactics. Ensure your plan is accessible even during a network outage - consider storing it in the cloud or via mobile apps. With BEC alone causing $2.77 billion in losses in 2024, regular testing and updates are essential to avoid becoming part of that statistic.
Frequent testing and timely updates ensure your email API incident response plan remains effective and compliant with regulatory requirements.
Using the Email Service Business Directory to Find Secure Email API Providers

When it comes to incident response planning, picking a secure email provider is a critical step.
How the Email Service Business Directory Helps
Finding a secure email API provider isn’t just about ensuring emails are delivered - it’s about safeguarding your data and being ready to handle potential security incidents. The Email Service Business Directory simplifies this process by letting businesses compare providers based on essential security certifications like ISO 27001 and SOC 2, as well as compliance with laws like GDPR and CCPA. Considering that security breaches surged by 75% in 2024, with organizations enduring an average of 1,876 cyberattacks per quarter, this tool helps save time and reduces risks by focusing on these critical factors.
The directory also highlights providers that integrate advanced threat detection tools. This makes it easier to spot platforms offering key features like automated account isolation, malicious IP blocking, and forensic support - all of which are vital for building a strong incident response strategy. Instead of spending hours researching each provider, the directory consolidates all this information, making side-by-side evaluations simple. This streamlined approach helps organizations adopt a proactive stance when preparing for potential security threats.
Choosing Providers with Incident Response Features
It’s essential to prioritize providers that offer AI-powered threat detection capable of learning normal behavior patterns and automatically blocking anomalies, such as phishing attempts. This aligns with strategies for containing breaches early. As Mick Leach from the Incident Response Planning Team explains:
AI-based detection systems use algorithms to learn and define normal behavior, then block emails that deviate from that pattern.
Additionally, look for providers that offer comprehensive logging and audit trails for evidence collection. Support for protocols like SPF, DKIM, DMARC, and TLS is equally important to prevent email spoofing. With 94% of organizations facing significant email security risks and phishing attacks, these features are non-negotiable.
Another must-have is multi-factor authentication (MFA) for administrative access, along with an auditable chain of custody to assist with legal matters if needed. As data breaches are projected to cost an average of $3.87 million in 2025, choosing a provider with robust incident response tools is a smart investment. The directory simplifies this process by spotlighting platforms with advanced monitoring, automated containment, and strong deliverability - all of which help maintain business continuity during a breach. Opting for providers with these capabilities strengthens your overall incident response plan.
Conclusion
Breaches are an unavoidable reality. Since 2013, the FBI has reported nearly $51 billion in losses from business email compromise, with a staggering $2.77 billion lost in 2024 alone. These figures highlight the urgent need for preparation. As Mick Leach from Abnormal Security aptly states:
What you do when you first discover the attack will decide how costly and far-reaching the damage is.
Having a clear incident response plan in place can make all the difference, especially in the critical first 15 minutes of a breach. It eliminates confusion and ensures swift, decisive action when it matters most.
Beyond planning, regular testing is key. Quarterly tabletop exercises can expose weaknesses in your workflows and ensure everyone knows their role during a crisis. These simulations shift plans from theory to practice, helping teams identify and fix gaps before a real attack strikes.
Choosing the right email API provider is another essential step in strengthening your defenses. With security breaches up by 75% in 2024 and organizations facing an average of 1,876 attacks per quarter, it’s crucial to select providers offering advanced features like AI-driven threat detection, automated containment, and compliance with notification regulations. The Email Service Business Directory simplifies this process, pointing you toward platforms equipped with these critical capabilities, saving time and reducing risk.
As cybercriminals increasingly use generative AI for sophisticated attacks like deepfakes, it’s vital to keep your incident response plan updated annually and test it quarterly. Define roles clearly across teams, from IT to legal, to ensure a unified response. With the average data breach projected to cost $3.87 million in 2025, investing in preparation now can help minimize future losses. This proactive approach ensures your organization is ready to face an ever-changing threat landscape.
FAQs
What should we do in the first 15 minutes of an email API breach?
The first step is to isolate the affected systems. Disconnect them from the network immediately to prevent further spread, but make sure not to delete any files - this is crucial for preserving forensic evidence.
Next, notify your incident response team. This includes key personnel such as IT specialists, legal advisors, and communications leads. Their involvement ensures a coordinated approach to managing the situation.
Finally, preserve all logs and evidence. These records will be critical for understanding what happened and planning the next steps. By acting quickly and carefully, you can limit the damage, protect vital data, and set the stage for a thorough investigation and effective remediation.
How do we determine if an incident is SEV-1, SEV-2, SEV-3, or SEV-4?
Incident severity levels categorize issues based on their impact on users and business operations.
- SEV-1: This is the most critical level, typically involving major outages that affect a large portion of users or core business functions.
- SEV-4: At the other end of the spectrum, this level covers minor issues that have a low impact on operations.
These classifications are crucial for helping teams focus their response efforts where they are needed most, ensuring critical problems get addressed quickly while less urgent matters are handled appropriately.
What logs and evidence should we capture for an email API incident?
To thoroughly investigate and address incidents, gather detailed event logs such as audit logs, API activity logs, email message IDs, and response codes. Additionally, collect supporting evidence like email headers, precise timestamps, and any error messages tied to the event. These details are crucial for pinpointing malicious actions, understanding the breach, and crafting an effective response.


